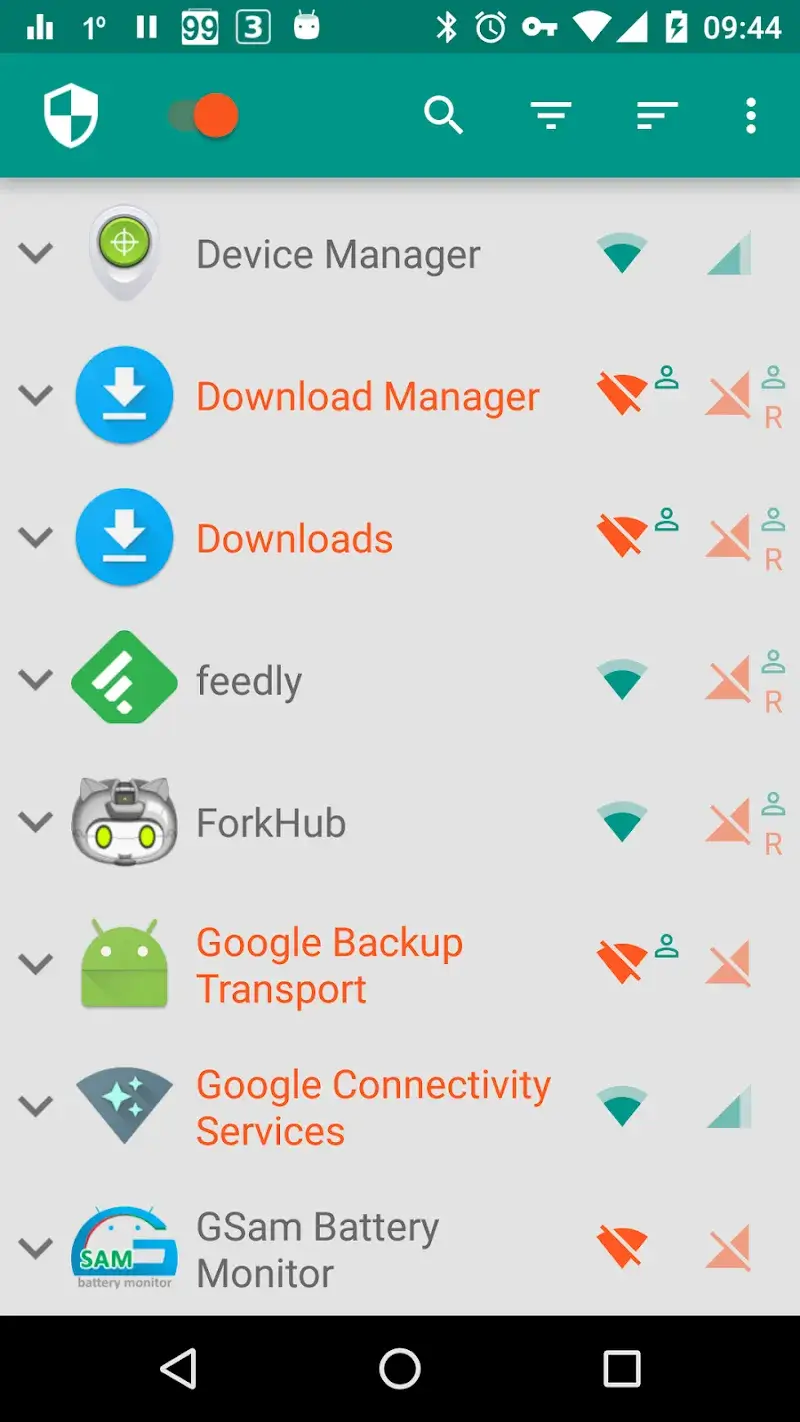
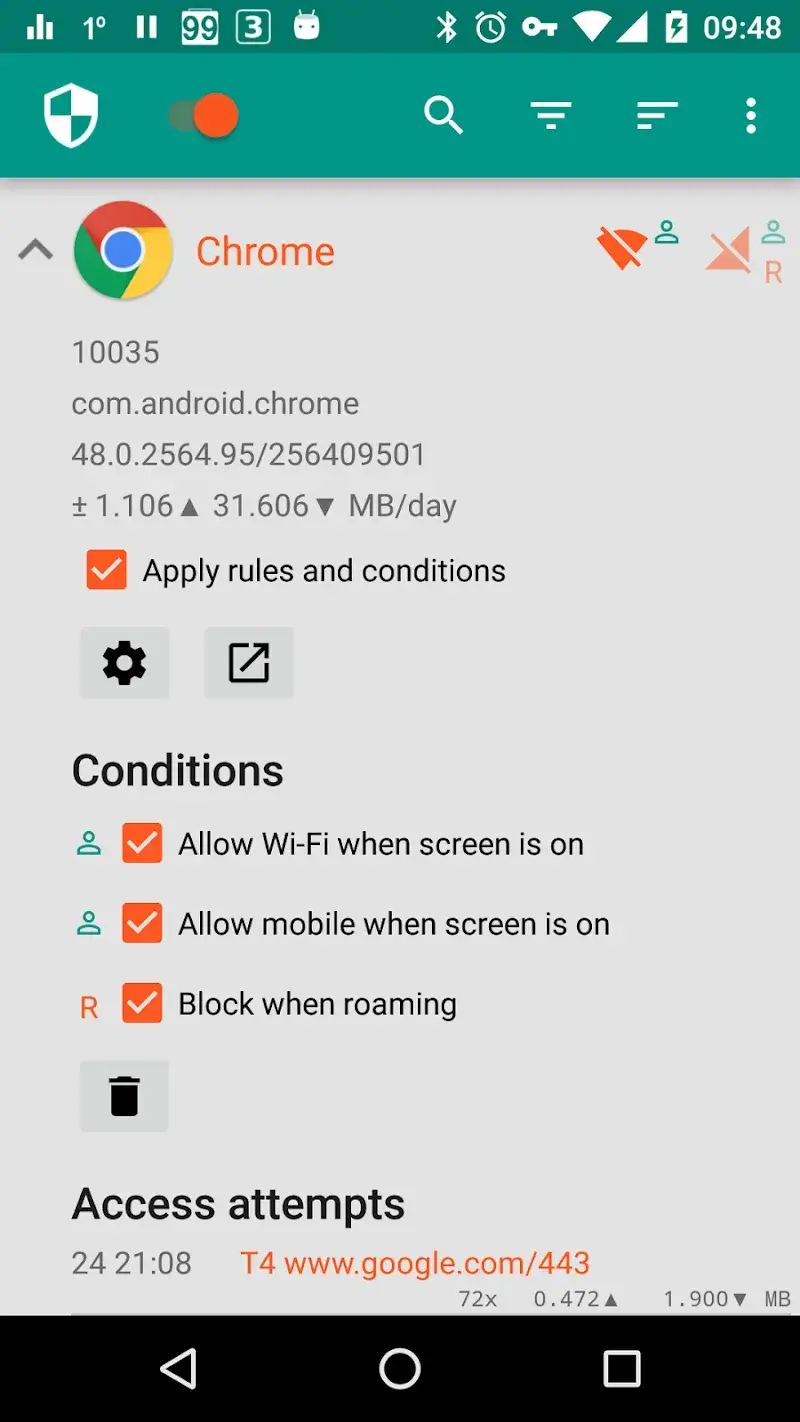
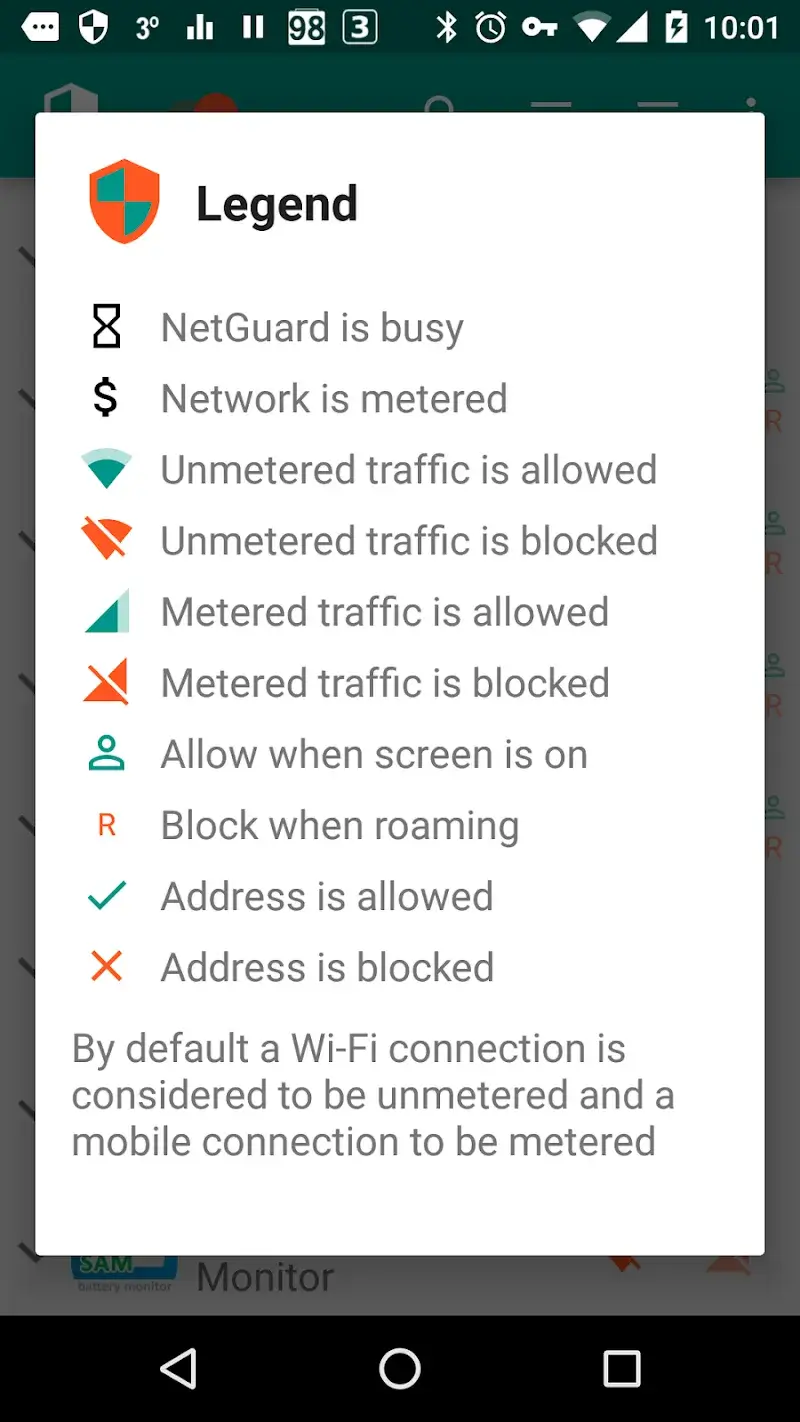
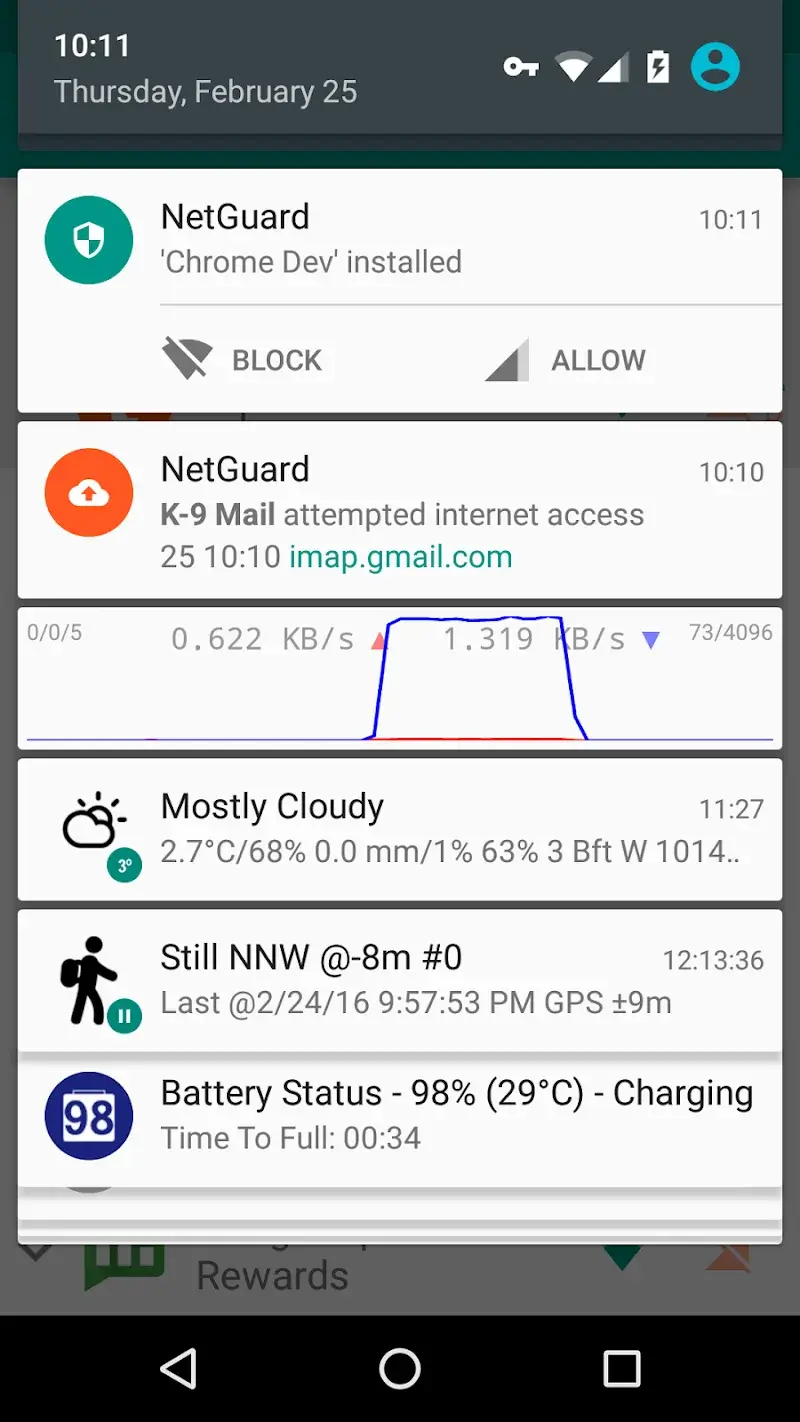
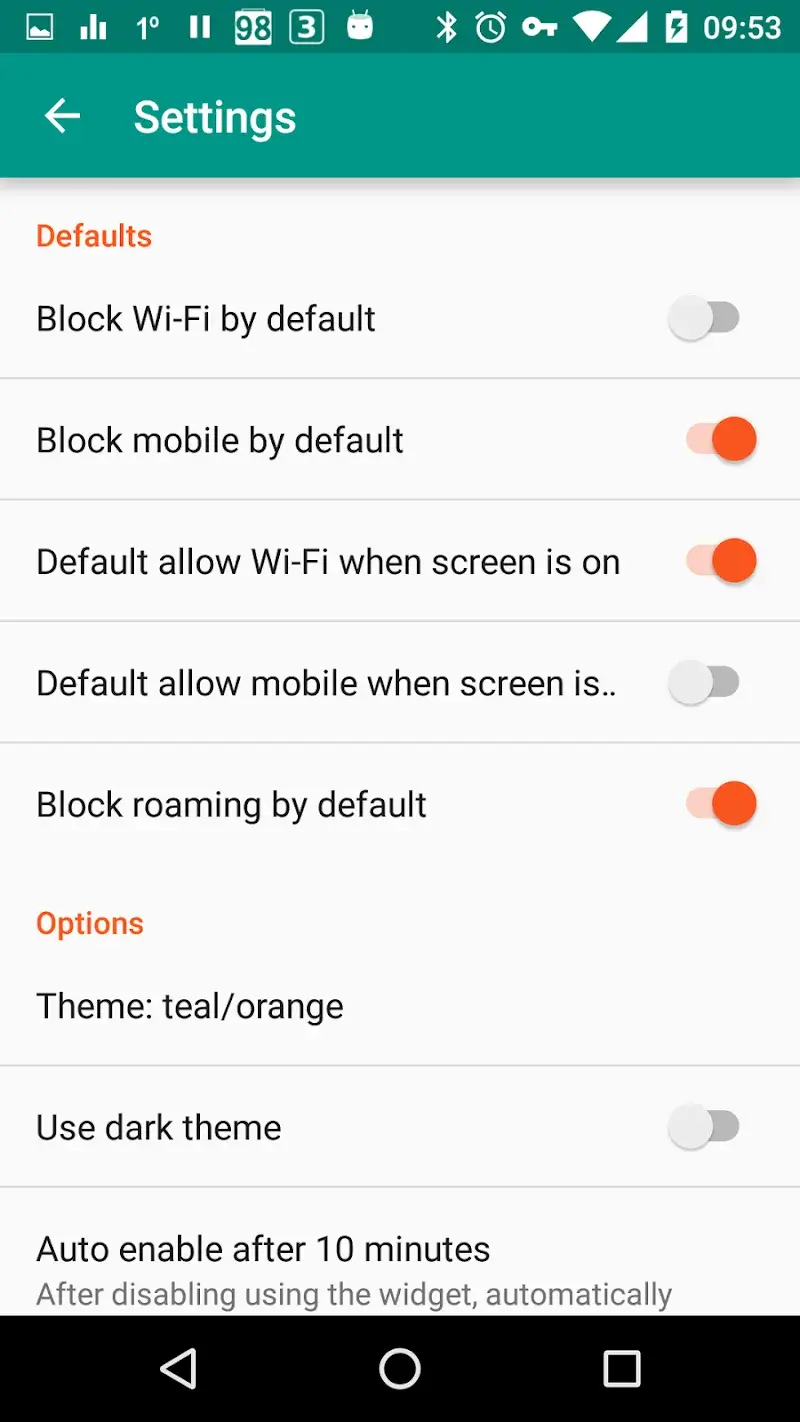
NetGuard - no-root firewall Mod is a network-level application firewall for Android that operates without requiring root privileges. It functions by creating a local VPN tunnel to intercept and filter all network traffic from other apps on the device. The target user is a privacy-conscious power user or developer who needs granular control over which applications can access the internet, via Wi-Fi or mobile data, for purposes of data conservation, battery saving, or security.
What This Mod Unlocks
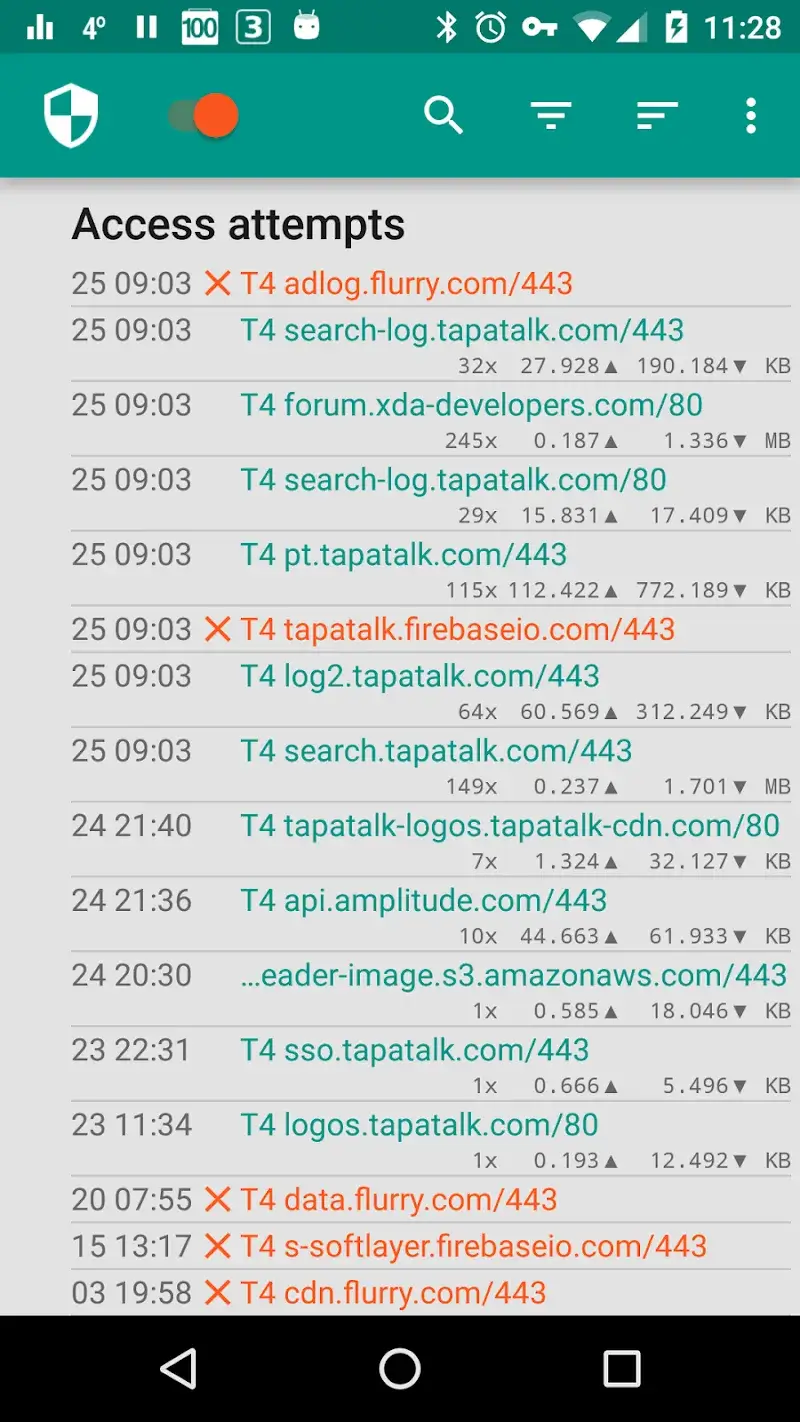
- Pro features unlocked, including advanced filtering rules based on IP address, domain, and port.
- Ad blocking functionality is enabled, allowing system-wide blocking of known ad servers.
- Traffic logging to a local file is now available for detailed analysis.
- Access to allow/deny rules for individual system applications is unlocked.
- The ability to filter traffic based on specific destination ports is activated.
- Support for custom DNS servers within the firewall configuration is enabled.
The primary mod feature, the Pro unlock, is automatically applied upon the first launch of NetGuard - no-root firewall Mod. No activation menu or specific tap sequence is required; the app will present the full set of Pro options in its settings and rule configuration screens immediately.
The application requires Android 5.1 or higher. It does not require root access. Storage requirements are minimal, approximately 10 MB for the APK installation plus additional space for traffic logs if that feature is utilized.
Installation follows the standard sideload process for modified APKs. First, enable installation from unknown sources in the device's security settings. Second, download the modded NetGuard - no-root firewall Mod APK file. Third, locate the downloaded file using a file manager and tap to install. Fourth, launch the application and grant the necessary VPN permission when prompted.
There are known edge cases. The VPN-based method means other VPN services cannot be used concurrently. Some deeply integrated system apps may bypass the firewall's detection. Filtering rules and logs are stored locally and will be lost if the app's data is cleared. Using the ad-blocking feature in online games or apps with strict anti-cheat systems could potentially lead to detection, though this is uncommon for a firewall utility.